On Friday, the United States imposed sanctions on two Israeli entities that had been...
Baldur’s Gate 3, which was released last summer, has been met with critical acclaim...
Companies often draw inspiration from current events and real-life situations for their advertising and...
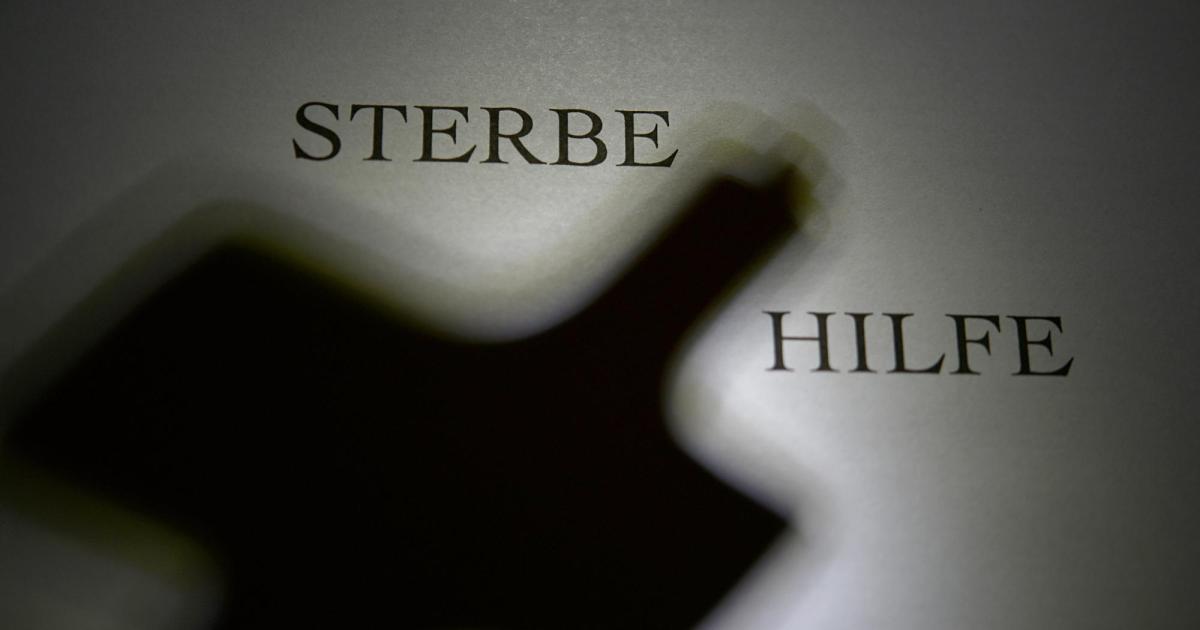
Gary Drake, a terminally ill individual who had traveled to Oregon to end his...
London police announced on Thursday that they had successfully infiltrated a criminal network known...
Luba Yammine, an addiction researcher, has suggested that the part of the brain responsible...
In recent news, the Rural Mainstreet Index has fallen below growth neutral for the...
The United States has appointed John Hynes as the head coach for their men’s...
In 2023, the video game market in Italy experienced positive growth, surpassing 2.3 billion...
Colorado is facing a statewide congenital syphilis epidemic, with an alarming spike in cases...



:quality(75)/cloudfront-us-east-1.images.arcpublishing.com/elcomercio/6K33TQCFEBGQ3JHB35M7HS3SSA.jpg)




